 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Beim Rowhammer-Angriff klöppelt der Angreifer so lange auf einem Speicherbereich rum, bis benachbarte Bits flippen. So kann man Systeme lahmlegen und sich sogar Admin-Rechte verschaffen. Unglaublicherweise klappt das auch mit JavaScript über das Internet.
Im März schlug die Veröffentlichung einer Reihe von Google-Forscher große Wellen: Auf DRAM-Chips lassen sich mit Gewalt Bits flippen und Angreifer können so den Rechner des Opfers abstürzen lassen oder gar Admin-Rechte erlangen. Jetzt haben Forscher der Technischen Universität Graz und der Firma Technicolor es geschafft,den sogenannten Rowhammer-Angriff auf JavaScript zu übertragen.
Damit kann man den Speicher aus der Ferne malträtieren, wenn das Opfer eine präparierte Webseite besucht. Die Gefahr eines gezielten Angriffs im Alltag ist zwar nach wie vor begrenzt, wenn es dem Angreifer aber nur darum geht, Daten in den Systemen zu verfälschen oder diese zum Absturz zu bringen, so ist dem Tür und Tor geöffnet und zwar nicht etwa nur für x86, sondern prinzipiell auch für ARM und andere Architekturen.
Mehr erfahren / Learn more:
https://gustmees.wordpress.com/2014/08/24/coding-a-new-trend-in-education-and-a-big-responsibility/

|
Scooped by
Gust MEES
|
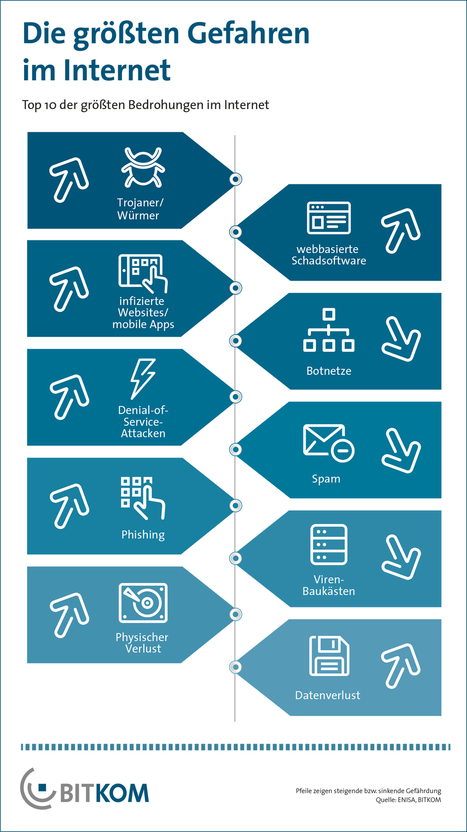
Gefahr für die IT-Sicherheit von Unternehmen: Die Nachrichten sind voller Meldungen über mehr oder weniger erfolgreiche Hacker-Angriffe auf Unternehmen und Behörden. Schnell entsteht dadurch der Eindruck, dass eine Gefahr vor allem von außen droht. Das Gegenteil ist jedoch der Fall.
Cyber-Gefahr: Nur 45 Prozent der Angriffe auf Unternehmen kommen von externen Hackern.
(Quelle: IBM )„Wir sprechen viel darüber, dass Cyberattacken das Werk anonymer Profihacker sind, die mit ihrem Laptop fernab in irgendwelchen dunklen Ecken sitzen und auf eine Gelegenheit warten“, sagt der IBM-Sicherheitsexperte Gerd Rademann. „Was jedoch kaum wahrgenommen wird: Über die Hälfte der Angriffe kommen aus den eigenen Reihen oder von Dritten mit Systemzugriff – also von Insidern.“
Mehr erfahren / Learn more:
- https://gustmees.wordpress.com/2012/07/11/cyberhygiene-hygiene-for-ict-in-education-and-business/

|
Scooped by
Gust MEES
|
Next Generation Firewalls (NGFWs) ermöglichen eine Kontrolle über die in Unternehmen genutzten Applikationen. Sie sind die Antwort auf immer professionellere Angriffe durch Cyber-Kriminelle.

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Des chercheurs ont découvert un outil d'attaque web qui permet à des pirates de détourner les serveurs DNS des routeurs et de les remplacer par des serveurs voyous.
Des cybercriminels ont développé un outil d'attaque web à grande échelle qui leur permet d’exploiter les vulnérabilités des routeurs et de détourner leurs paramètres DNS quand les utilisateurs visitent des sites web compromis ou sont dirigés vers des publicités malveillantes depuis leurs navigateurs. L’objectif de ces attaques est de remplacer les serveurs DNS configurés sur les routeurs par des serveurs voyous contrôlés par des attaquants.
Ainsi, les pirates peuvent intercepter le trafic, le rediriger vers des sites frauduleux, détourner les requêtes de recherche, injecter des publicités malveillantes sur les pages web et plus encore.
Learn more / En savoir plus:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Router

|
Scooped by
Gust MEES
|
Businesses often don't realise why encryption is important, and how they can use it to protect their data. The latest in our Practical IT series tells you what encryption is and how you can use it ...
What is encryption? Encryption is a method of scrambling messages in a format that is unreadable by unauthorised users - it is, simply put, the best way to keep data secure from spies, thieves or accidental exposure. (Not to be confused with steganography, which is all about hiding messages, rather than making them unreadable).

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
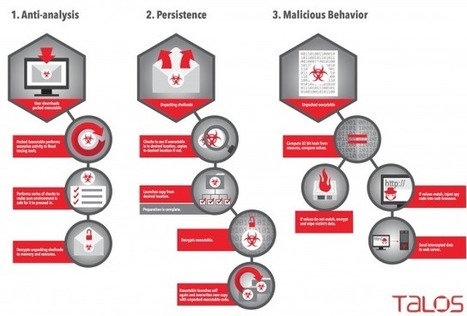
The game of cat-and-mouse between malware authors and security white hats may have entered a new phase this week, thanks to an aggressive new malware system that doesn’t just attempt to obfuscate its own operation — it aggressively scans for clues that others are monitoring its actions. If it detects that it’s operating within a Virtual Machine, the malware, dubbed Rombertik, will go nuclear and attempt to overwrite the master boot record of the local hard drive.
Cisco’s threat response team has detailed the operation of Rombertik, and the malware’s obfuscation and attack vectors are unique. Once installed, it’s a fairly standard data sniffer that grabs indiscriminately from the information available on an infected PC. What sets Rombertik apart is the way it checks to see if it’s running in a VM-provided sandbox, and the actions it takes if it finds itself in such a mode.
Learn more:
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Rombertik

|
Scooped by
Gust MEES
|
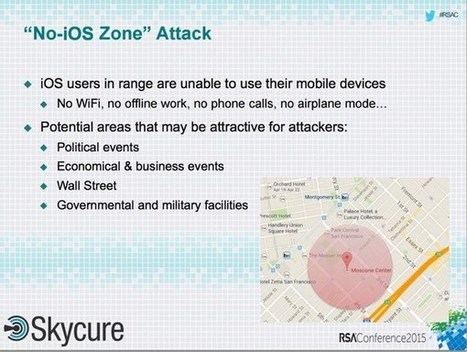
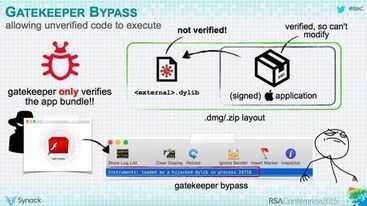
"No iOS Zone" denial-of-service vulnerability could lead to your iPhone or iPad constantly crashing.
The researchers say that they first informed Apple of the problem in early October 2014, and that iOS 8.3 appears to resolve some of the issues they uncovered.
Chances are that this won’t be the last time that a serious denial of service flaw is found in iOS. Just last month, Apple released iOS 8.2 which fixed a flaw that allowed hackers to restart iPhones by sending them a maliciously-crafted Flash SMS.
More details of the “No iOS Zone” flaw can be found in the slide deck of the presentation given at the RSA conference.

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Der sorglose Umgang der Mitarbeiter mit mobiler Technologie gehört laut IDC neben Malware und Phishing-Attacken zu den häufigsten Risiken beim Thema Mobile Security in Unternehmen.
Zu den größten Sicherheitsrisiken aus Sicht der IT-Verantwortlichen zählen dabei Mobile Malware mit 42 Prozent, gefolgt von Phishing und Social Engineering mit 35 Prozent. Weitere 30 Prozent gaben an, dass das Fehlverhalten von Anwendern – vorsätzlich oder unabsichtlich – ein großes Risiko darstelle. Sie planen deshalb, die Mitarbeiter stärker für das Thema Mobile Security zu sensibilisieren. Dies soll vor allem durch Trainings der Anwender und IT-Mitarbeiter sowie Richtlinien zur sicheren Nutzung mobiler Endgeräte geschehen - wobei hier die Wünsche der IT-Verantwortlichen und der User teils sehr unterschiedlich sind. . Learn more / Mehr erfahren: . .

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Cyber security is no longer the sole responsibility of the technical people, or even the CIO.
Following the Target breach (where immense pressure was placed to replace most of the board members after the breach), and board members of Target and Wyndham Worldwide (hotel chain) face derivative lawsuit related to the data breaches. Recent survey reveal that nearly half (45%) of senior management acknowledge that the C-suite and senior leadership themselves are responsible for protecting their companies against cyber-attacks, and the U.S. Securities and Exchange Commission recently published a paper on the Role of the Boards of Directors in Overseeing Cyber-Risk Management, where it recommends:
Cyber-risk must be considered as part of the board’s overall risk oversight: “boards that choose to ignore, or minimize, the importance of cyber security oversight responsibility, do so at their own peril.”
Boards should assess the corporation’s cyber security measures including corporate policies and annual budgets for privacy and IT security programs. And perhaps, more critically, highlights the significance of cyber-risk education for directors, ensuring that the board be at least adequately represented by members with a good understanding of information technology issues that pose risks to the company.
Learn more:
- http://www.sec.gov/News/Speech/Detail/Speech/1370542057946
- https://gustmees.wordpress.com/2012/10/11/learning-basics-of-cyber-security-by-easy-to-follow-steps/
- https://gustmees.wordpress.com/2012/11/29/cyber-hygiene-ict-hygiene-for-population-education-and-business/
- https://gustmees.wordpress.com/2012/07/11/cyberhygiene-hygiene-for-ict-in-education-and-business/

|
Scooped by
Gust MEES
|
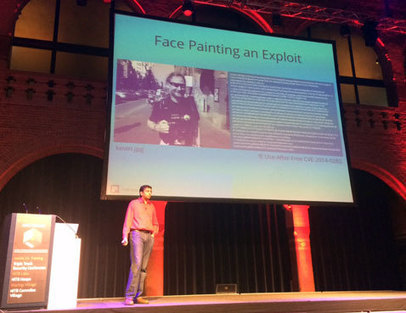
Successfully hiding messages in images has already been done, but is it possible to deliver an exploit in one - and run it?
Saumil Shah, founder and CEO of Net-Square, has demonstrated at the Hack in the Box Amsterdam 2015 that it's possible, and has posited that such attacks are more than likely to crop up in the near future, as he can't be the only one who thought about this, tried it and succeeded.
He is not the first one to try and hide exploits in images. But he created Stegosploit, a technology that lets attackers deliver executable JavaScript code via images, and trigger them, too.
The technology opens the door for attacks executed as simply as pointing users to sites containing a booby-trapped image or delivering the image via email. By virtue of simply viewing the image, the exploit code is triggered and can deliver malware on the victim's computer.
"A single file can be rendered as a perfectly valid HTML file, executed as a perfectly valid Javascript file, and displayed as a perfectly valid image, all at the same time," he explains.
"Stegosploit is the result of malicious exploit code hidden within pixels of the image carrying it. The image however, is a multi format container, which also contains the code required to decode the steganographically encoded pixels to execute the exploit."
This type of attack won't show in network traffic, he pointed out, be invisible to the naked eye, and the image will "autorun" in the browser.
In order to make the attack payload look harmless and not trigger defenses, Shah split it into two: dangerous pixel data (exploit code), and a safe decoder.

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Rombertik is designed to steal any plain text entered into a browser window
A new type of malware resorts to crippling a computer if it is detected during security checks, a particularly catastrophic blow to its victims. The malware, nicknamed Rombertik by Cisco Systems, is designed to intercept any plain text entered into a browser window. It is being spread through spam and phishing messages, according to Cisco’s Talos Group blog on Monday.
Rombertik goes through several checks once it is up and running on a Windows computer to see if it has been detected. That behavior is not unusual for some types of malware, but Rombertik “is unique in that it actively attempts to destroy the computer if it detects certain attributes associated with malware analysis,” wrote Ben Baker and Alex Chiu of the Talos Group.
Such “wiper” malware has been used in the past, notably against South Korean targets in 2013 and against Sony Pictures Entertainment last year, an attack attributed to North Korea by the U.S. government. The last check Rombertik does is the most dangerous one. It computes a 32-bit hash of a resource in memory, and if either that resource or the compile time had been changed, Rombertik triggers self-destruct.
Learn more:
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Rombertik

|
Scooped by
Gust MEES
|
Here they are: the latest "Dirty Dozen" SPAMPIONSHIP tables, detailing the globe's most dastardly distributors of delinquent data during the first quarter of 2015.
If you haven't seen the Dirty Dozen before, here's how it works.
SophosLabs maintains a large network of spamtraps, operated around the world with the express purpose of collecting spam.
And, boy, do they collect spam!
Of course, whenever spam falls into a trap, we can tell where the final step of its journey started by looking at the IP address of the computer from which the offending email was sent.
It's possible to track back individual IP numbers fairly accurately, sometimes down to a street block, often to a suburb or metro area, and almost always to the sender's country.
In other words, our spamtraps tell us which countries are the worst senders of spam.
Learn more:
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Spam
- https://gustmeesen.wordpress.com/2012/01/07/pc-security-howto-fight-spam-efficiently/

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Drop-dead simple advice on keeping intruders' hands off your account, spotting phishing attempts and more.
To do that, it's added a new security collection called How to Keep Your Account Secure to the Privacy Basics page. The topics cover setting a strong password, spotting attempts to steal passwords and other info, details on how Facebook handles government requests for information, and advice on what to do if your account gets hijacked.

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...











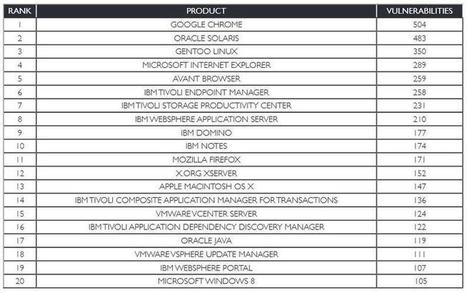




![8 Vulnerable Software Apps Exposing Your Computer to Cyber Attacks [Infographic] | CyberSecurity | eSkills | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/Manyk3R4XvcpHXxi11NTkTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)










Mehr erfahren / En savoir plus / Learning more:
https://gustmees.wordpress.com/2012/05/03/update-your-third-party-applications/
https://gustmees.wordpress.com/2012/05/02/get-smart-with-5-minutes-tutorialsit-securitypart-1-browsers/